In a recent advisory, Okta, a leading identity and access management services provider, sounded the alarm over a rise in credential stuffing attacks targeting online services. Let’s delve into the details of this warning and understand the implications.
Overview of the Threat
Okta reported a significant increase in the frequency and scale of credential stuffing attacks against online services in recent weeks. These attacks have been fuelled by the widespread availability of residential proxy services, lists of previously stolen credentials, and automation tools. The surge in attacks poses a severe threat to the security of user accounts and sensitive data.
Observations by Security Experts
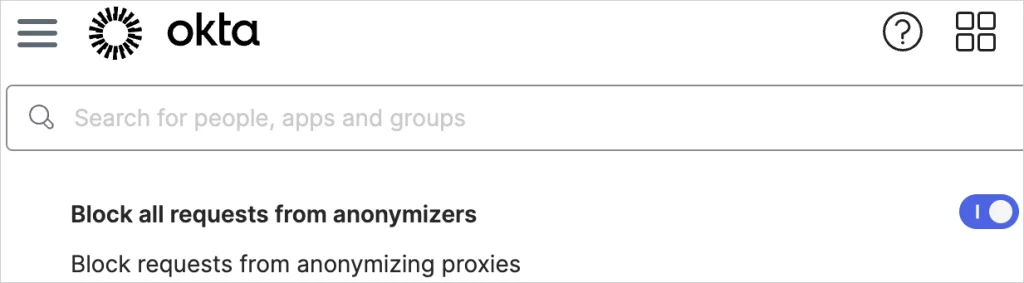
Duo Security and Cisco Talos also observed large-scale brute-force attacks against various targets, including VPN services, web application authentication interfaces, and SSH services. The attacks, originating from TOR exit nodes and other anonymizing tunnels and proxies, targeted VPN appliances and routers from multiple vendors.
Modus Operandi of Credential Stuffing Attacks
Credential stuffing attacks involve the automated trial of username and password combinations obtained from previous data breaches or phishing campaigns. Threat actors exploit the reuse of login credentials across multiple accounts, attempting to gain unauthorised access to compromised accounts.
Recommendations for Organisations
- Enable ThreatInsight in Log and Enforce Mode for proactive IP address blocking.
- Deny access from anonymizing proxies to prevent attacks from dubious sources.
- Switch to Okta Identity Engine for enhanced security features.
- Utilize CAPTCHA challenges and passwordless authentication with Okta FastPass.
- Implement Dynamic Zones to manage access based on geo-location and other criteria.
Okta
Implementing these recommendations can fortify an organisation’s defence against credential stuffing attacks, ensuring a safer online environment for users and stakeholders.
Conclusion
Credential stuffing attacks pose a significant threat to the security of online services and user accounts. By heeding Okta’s warning and implementing robust security measures, Okta customers can better protect themselves against these malicious activities and safeguard their sensitive data.
Another approach to create a safer cyber world is to not use the typical password based authentication. By eliminating passwords, organizations can improve their defences, increase security and reduce the risk of future incidents. Typical cyber attacks such as Credential Stuffing are not applicable to Passwordless authentication, so the best way to move forward is to #gopasswordless