Connect with Us!
Subscribe to receive new blog post from PureID in your mail box
As reported by Zscaler in April 2020, a significant increase (about 85%) in phishing attacks were seen, targeting remote workers. Attackers had registered domains featuring Covid-19 related keywords such as “virus”, “vaccine” etc. in order to steal credentials, disseminate malware, most notably ransomware for conducting financial frauds.
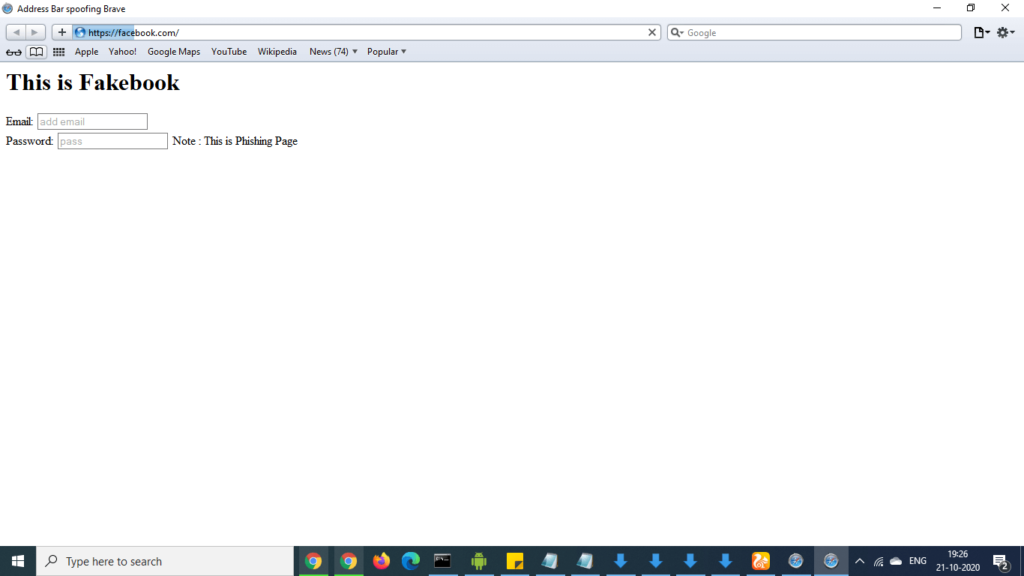
With ever-growing advanced spear-phishing attacks, vulnerabilities like Address Bar Spoofing make attacks more convincing and hard to distinguish. Cybersecurity researchers on Tuesday disclosed details about an address bar spoofing vulnerability affecting multiple mobile browsers.

These Vulnerabilities were first reported by pakistani researcher Rafay Baloch and Tod Bearsley of Rapid 7 in August 2020 and now the browser companies have started releasing its patches.
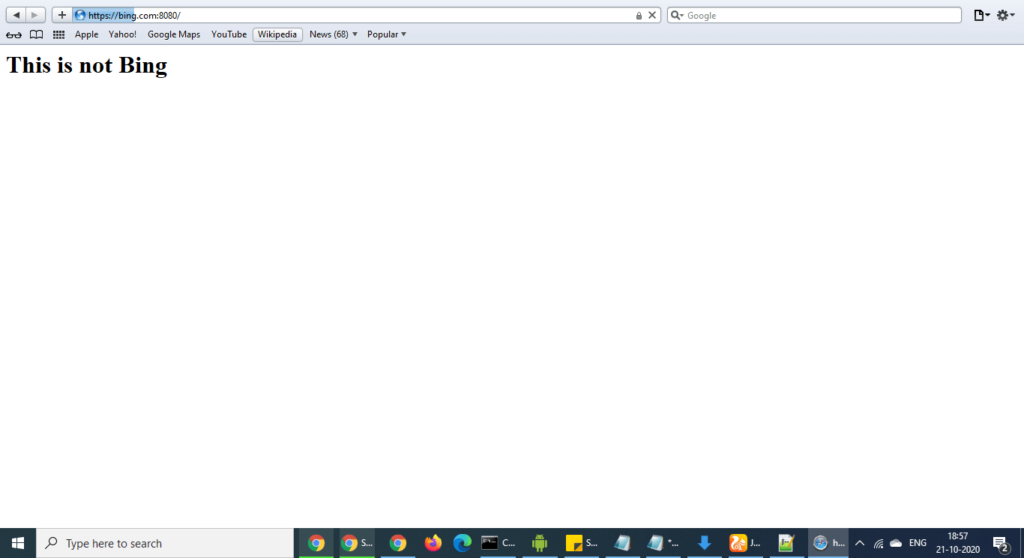
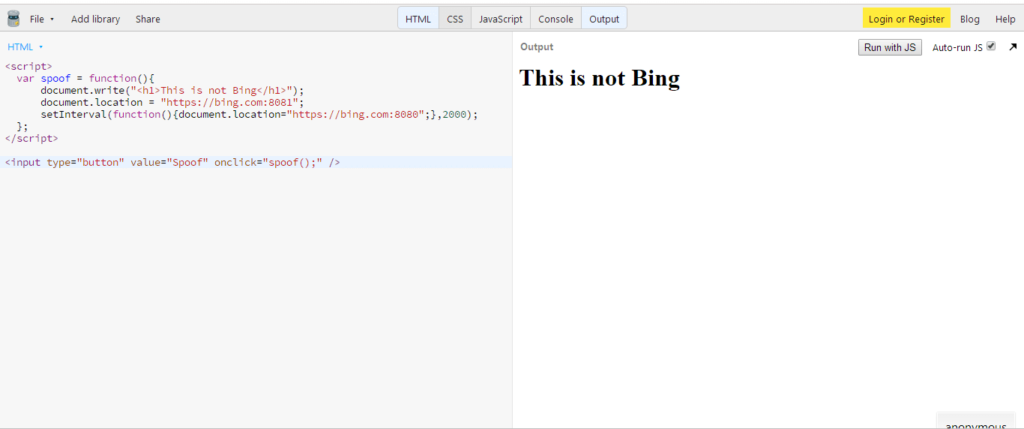
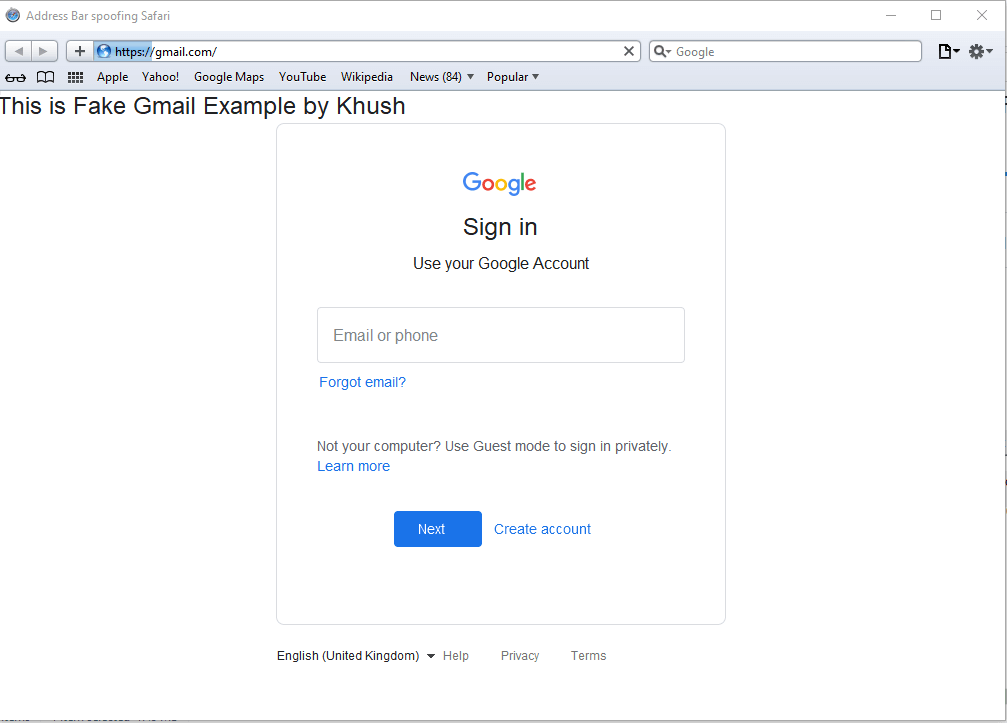
One can create a phishing link or a html page in which vulnerable browser will execute it in such a way that an attacker can set document.location to original domain so user will see original domain name loading in the vulnerable browser and he may end up entering his email and password thinking that the site is genuine. This is how an attacker can spoof address bars.
The vulnerability occurs due to Safari preserving the address bar of the URL when requested over an arbitrary port, the set interval function reloads bing.com:8080 every 2 milliseconds and hence user is unable to recognize the redirection from the original URL to spoofed URL. What makes this vulnerability more effective in Safari by default does not reveal port number in URL unless and until focus is set via cursor.
Our team has tested this successfully in Safari Version 5.1.7
Time and again it has been concluded in several breach investigation reports that Passwords are the #1 Target of hacker & Phishing is the Top most Risk for all the enterprises. The world is yet to find an effective solution for phishing/ spear-phishing attacks.
PureAUTH passwordless suites eliminate passwords from an enterprise and so does the threat of phishing/spear-phishing. Check out how we secure our users from in-mobile-phishing attacks with our best passwordless authentication solution.
Subscribe to receive new blog post from PureID in your mail box