Connect with Us!
Subscribe to receive new blog post from PureID in your mail box

Dropbox disclosed a security breach on October 14th 2022, resulted due to Phishing Emails. The email was impersonating a third-party service used by its employees. The attack resulted in credential leaks of employees, which enabled the threat actors access to their Github accounts. The hackers stole the content from 130 repositories, consisting information about Dropbox employees, users, and vendors.
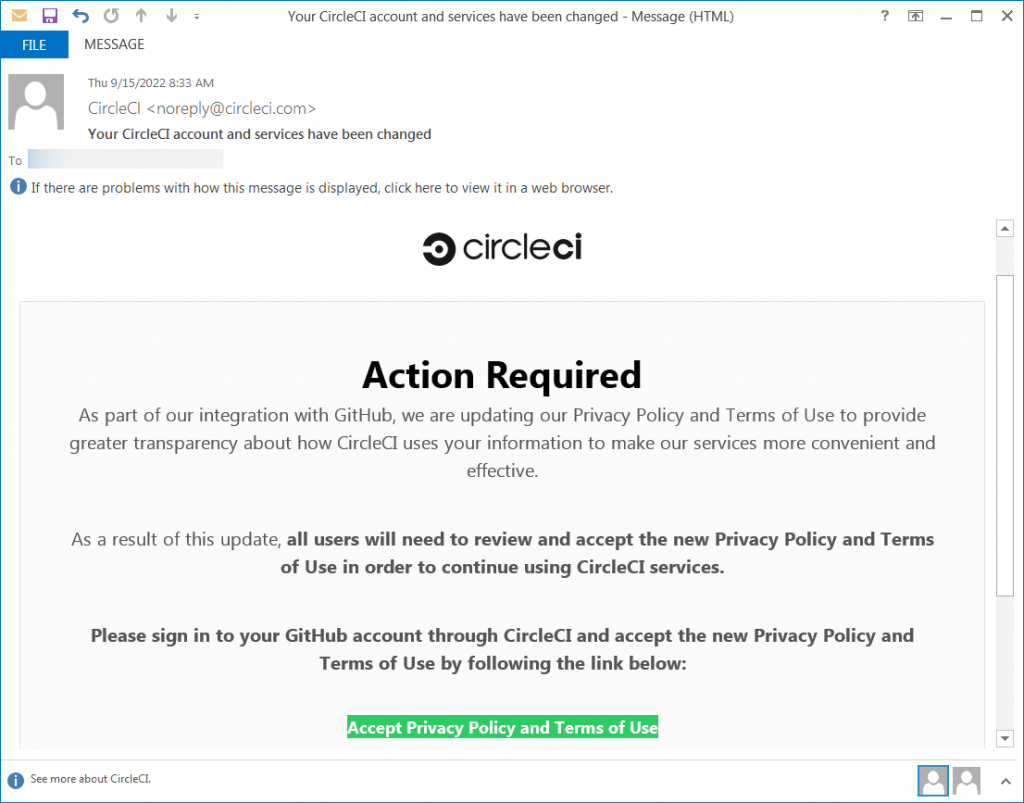
Phishing campaign initiated by adversary targeted multiple Dropbox Employees. The emails were crafted to mimic communication from CircleCI , which is a Continuous Integration and Delivery Platform. The phishing link redirected users to a landing page where they were asked to enter their GitHub username and password.
On a fake GitHub page, the employees were requested their Hardware Authentication Keys to provide an OTP for 2 step authentication. Adversaries used these credentials to access some less secure repositories of Dropbox, containing some API keys, and customised tools.
The adversaries are not traced yet, as they used VPNs to hide their tracks.
Dropbox breach is a direct result of phishing, which was not contained by 2FA or MFA solutions the firm normally has in place.
Furthermore, the laws of the United States allow authorities to have access to user data under Patriot Act and such, hence the firm can also store user information. In the past, there have been multiple instances at Dropbox where user data was compromised. However, in this particular case, the company is claiming that no core app code was compromised. For more details, visit here.
Dropbox is not the sole victim of brand impersonation phishing attacks. Earlier, other organisations such as Sony Pictures, BenefitMall, and JP Morgan Chase have fallen victim to the same. Furthermore US Power grid and John Podesta are also highly notable examples of Phishing Attacks.
IBM’s 2021 Cost of a Data Breach Report found phishing to be the second most expensive attack vector to contend with, costing organisations an average of $4.65 million. Phishing using brand impersonation is becoming quite popular as well. LinkedIn is used for this purpose 52% of the time, while DHL, Google, Microsoft and FedEx also hold a considerable proportion of it. You can find more about the stats here.
Millions of phishing emails are sent daily. Many spam mails slips through spam filters and when that happens, you must be able to rely on your employees to stay vigilant and act responsibly. That is the reason why many companies opt for Employee Awareness Training Plans.
When training campaigns cannot keep pace with the new trends, and URL-checking anti-phishing measures is proving to be far more intrusive. The best option right now is to switch to Password-less Systems with Zero Knowledge Encryption.
With PureAuth Password-less authentication, you can effectively mitigate the risk of having your password compromised by phishing and a number of other methods.
Feel free to explore further blogs by us related to Phishing and Github . Stay safe. #Gopasswordless
Subscribe to receive new blog post from PureID in your mail box